Managed Security Services
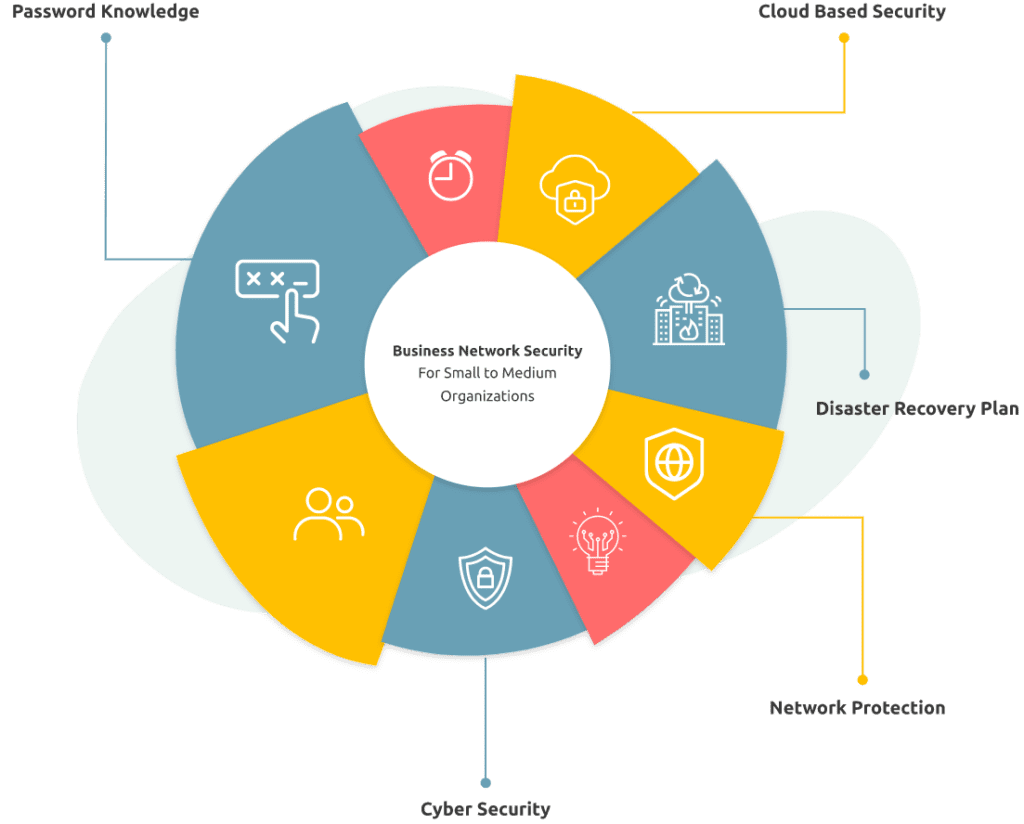
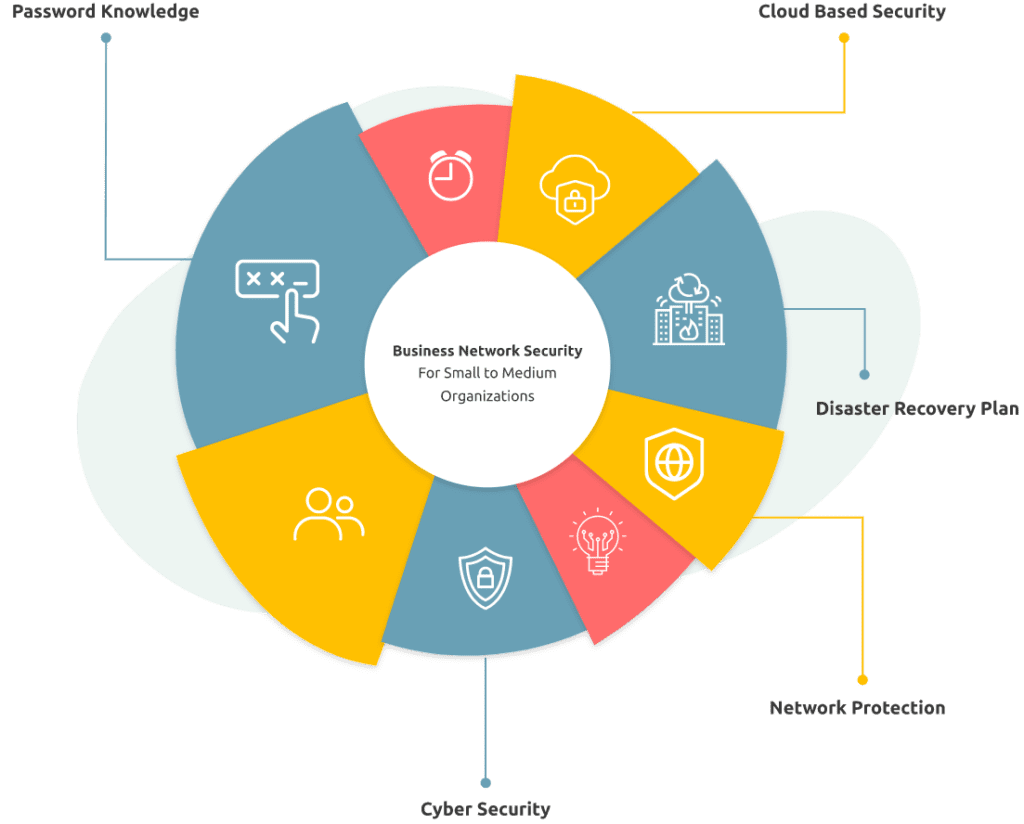
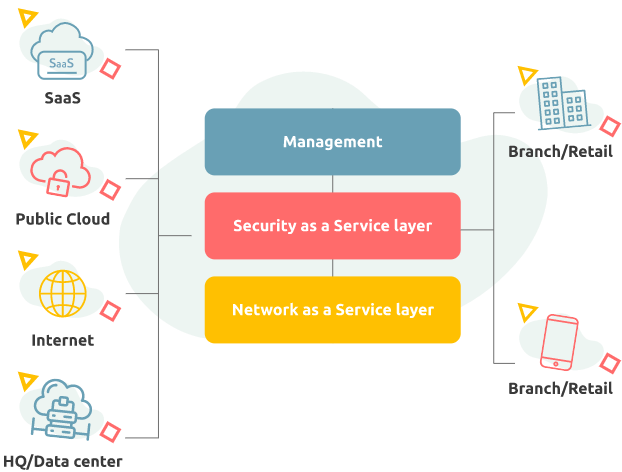
One prominent issue organisations face is the potential cost and complexity of managing everything in-house regarding network security.
Digital workplace services help IT unify endpoint and cloud security across your digital ecosystem. While ensuring the right users have access to applications on any network securely, it simplifies identity access management and optimises security operations.
You need a comprehensive solution that keeps your data secure, enables BYOD and other mobile solutions, and manages your in-house resources efficiently.
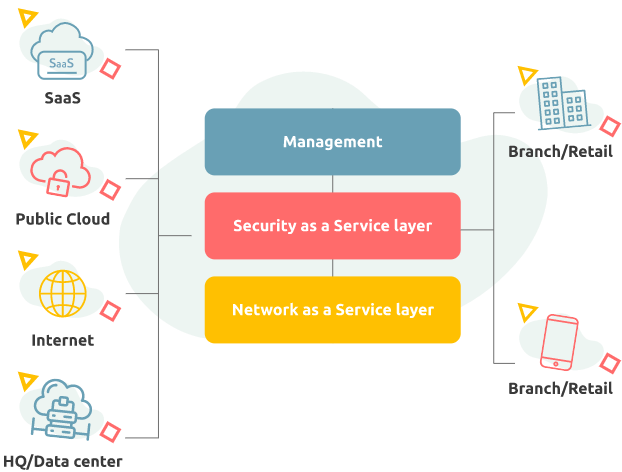
Managed Firewall Secure Connectivity
CloudI managed firewalls bundled with Internet solutions reduces the problem, easing the pressure on already stretched IT departments while providing our clients with the expertise they need to keep their business safe.
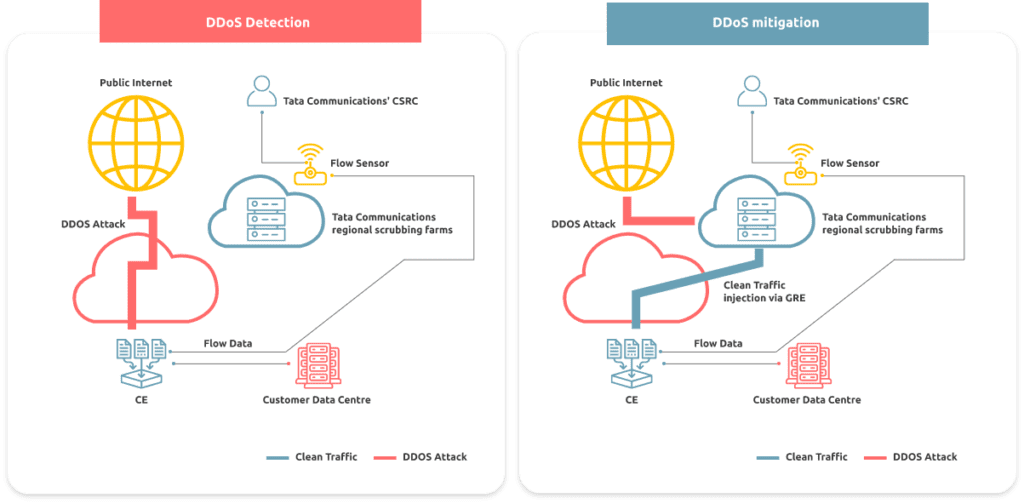
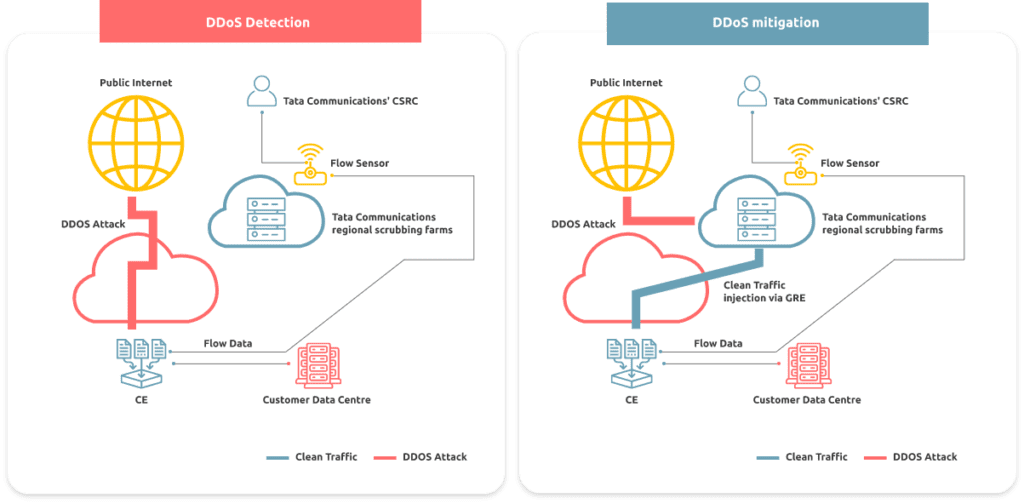
DDoS Protection Service
DDoS attacks target websites, hosted applications and network infrastructure by absorbing all available bandwidth. DDoS attackers overwhelm the application with malicious trac, often bringing systems and operations to a halt. This results in lost revenue opportunities, decreased productivity and damage to a company’s reputation
CloudI service scrutinises your network track in real time to identify anomalies and quarantine attack packets.Only malicious trac is blocked, while legitimate trac continues to flow so your network and applications remain always available to your legitimate users.
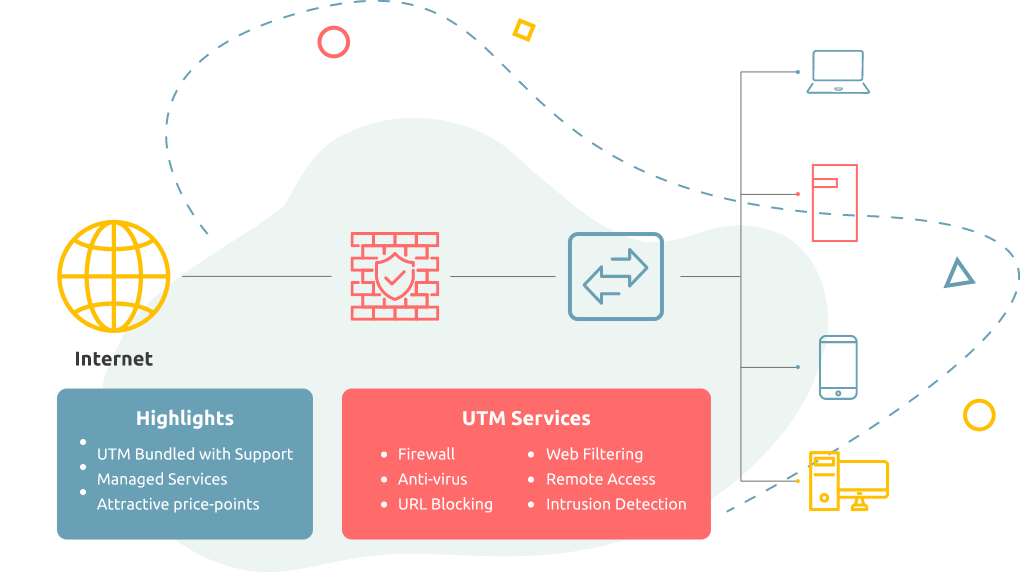
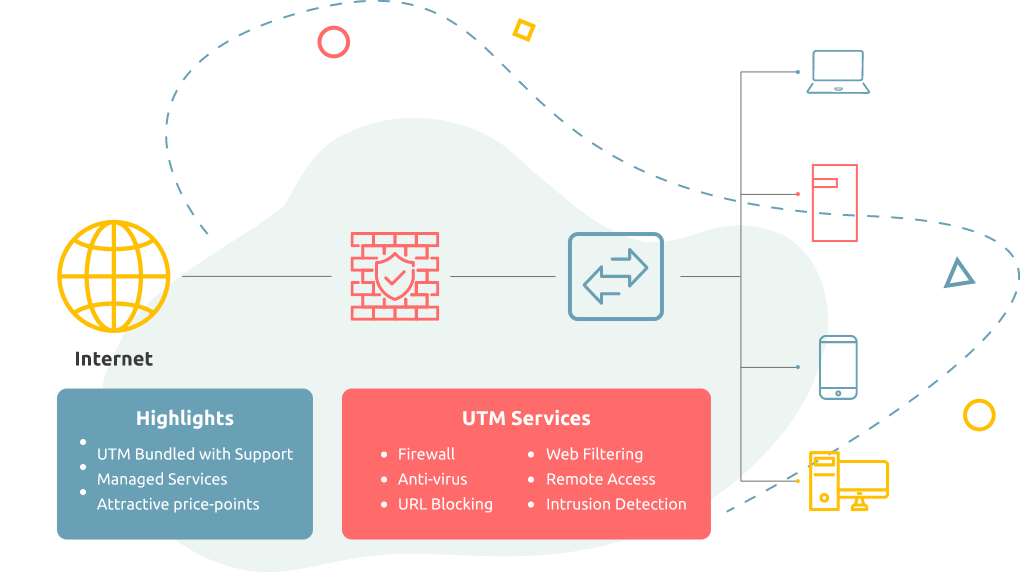
CloudI Unified Threat Management (UTM)
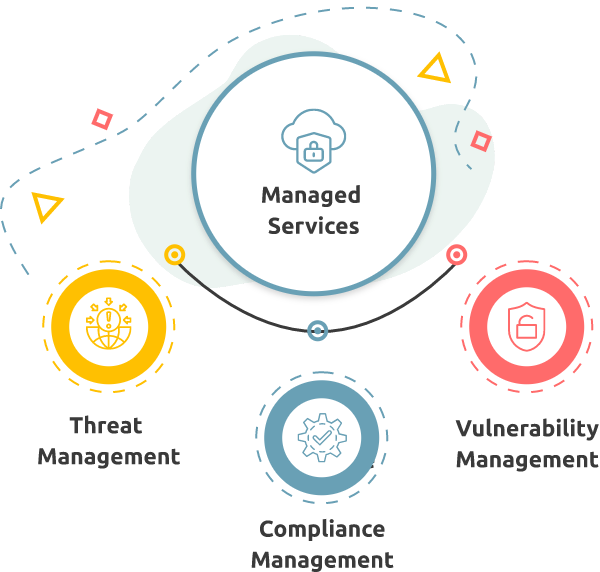
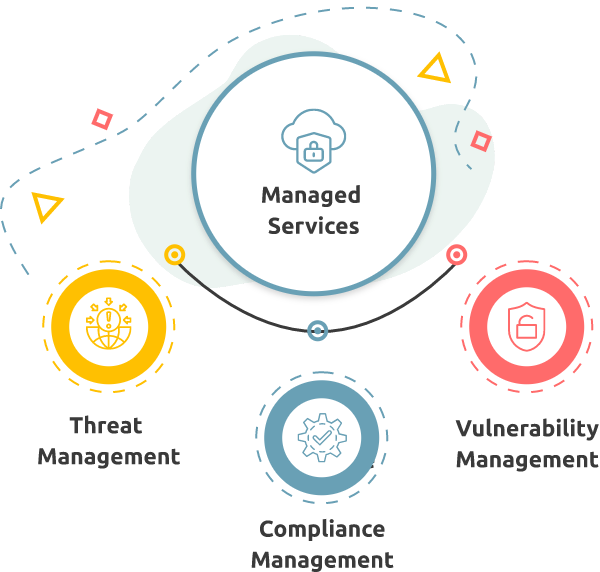
Cloudi Managed Security
Cloudi Managed Security Service (MSS) offers highly skilled managed security specialists and analysts who monitor your critical infrastructure and network security technologies 24×7. We combine our experience with leading technology to understand the threats you face, mitigate risk, and ensure business continuity by extending your team with a level of expertise that can be prohibitively expensive for organisations to hire internally.
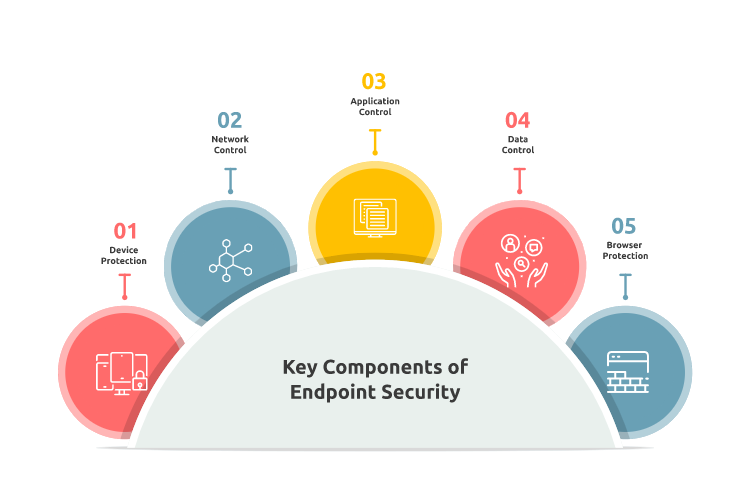
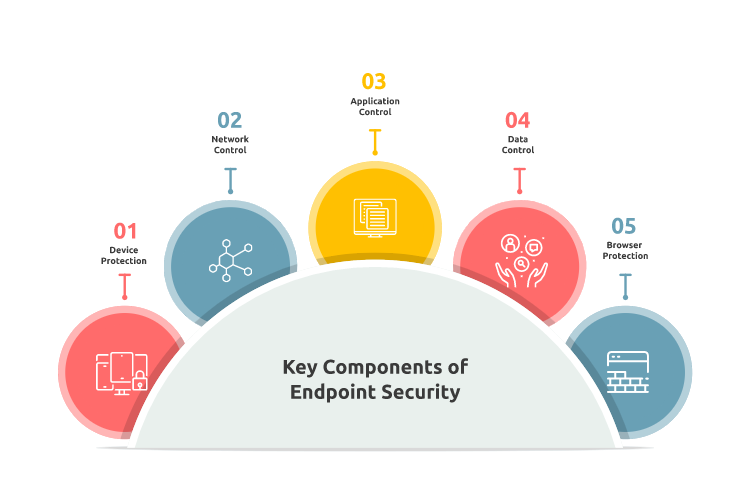
CloudI Endpoint Security
Endpoints are the weak links in an IT infrastructure and can cause information loss, corporate intellectual property theft, operational disruption and data breaches. Protect yourself from the threats that arise from these endpoints with our comprehensive endpoint security software. Our wide range of endpoint security services defends against advanced attacks like malware, ransomware, phishing, social engineering campaigns, and insider threats looking to steal intellectual property or company assets.
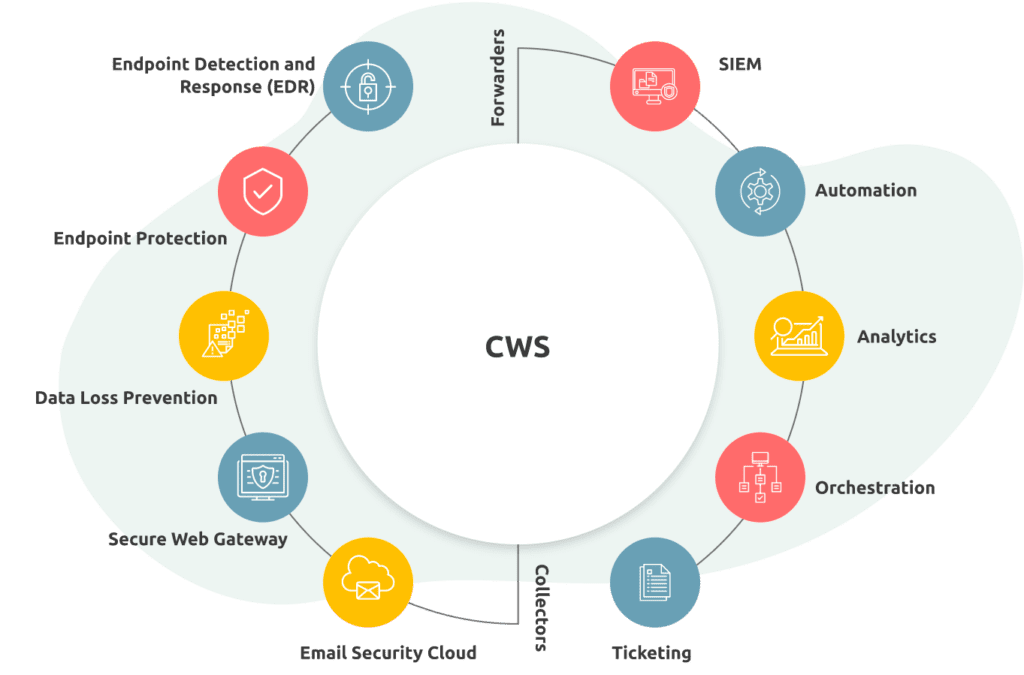
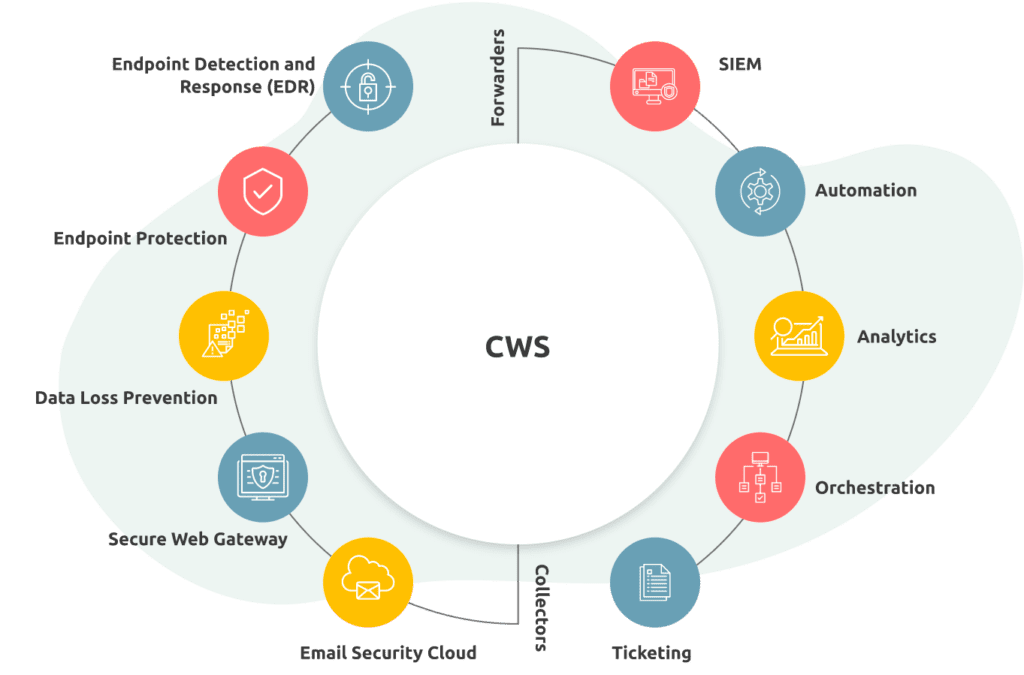
CloudI Virtual security operations centre
CloudI virtual security operations centre (vSOC) is a powerful tool that helps you manage your security posture and ensures the safety of your data. This centralised command and control centre offers ongoing, real-time monitoring of your enterprise, digging deep into your system logs and alerts to provide a holistic picture of your security. The vSOC helps you efficiently manage resources and respond to incidents, which is excellent for passing those pesky audits.


CloudI Web Security
CloudI Web Security is an enterprise-grade web security solution that offers complete visibility into internet activity, allowing you to enforce web usage policies and protect your network from online threats. Fast and reliable, Cloud Web Security improves employee productivity and protects your organisation from today’s advanced hazards by preventing infected devices from accessing your network and exfiltrating data.
Web Security provides real-time protection and thorough enforcement of web usage policies for the enterprise.The advanced protection you need to proactively and automatically detect, block and respond to the widening range of web-borne malware attacks.
CloudI Email Security
Limit your company’s email-related risks and raise productivity with our email security suite. Our cloud-based Email security protects all email platforms – Microsoft Exchange, Office 365, or on-premise servers. We are an advanced anti-phishing and malware engine.
Our cloud-based email security protects all email platforms – Microsoft Exchange, Office 365, or on-premise servers. We secure email from malware, ransomware, phishing, viruses, and spam, and also detect advanced persistent threats such as spear phishing, whaling, typo domain, and spoofing attacks.


Value Proposition
Vendor-agnostic.
Flexibility is one of our key advantages. We are not tied to any specific provider, so we can resort only to those tools and technologies that are a perfect fit for your project and workflows.
Service Level Agreement (SLA) adherence
With built-in redundancy,99.95% uptime is a critical aspect of our SLA, and this is achieved because of our strategic partners and highly dedicated team.
Security
CloudI-based security systems minimise IT risk for distributed-denial-of-service (DDoS) attacks and reduce downtime at the ISP end itself.


Reliability
Prioritise critical applications with customisable QoS



Installation and maintenance
Our technicians can install network equipment and provide ongoing maintenance, including 24/7 support.
Vendor-agnostic.
Flexibility is one of our key advantages. We are not tied to any specific provider, so we can resort only to those tools and technologies that are a perfect fit for your project and workflows.
Service Level Agreement (SLA) adherence
With built-in redundancy,99.95% uptime is a critical aspect of our SLA, and this is achieved because of our strategic partners and highly dedicated team.
Security
CloudI-based security systems minimise IT risk for distributed-denial-of-service (DDoS) attacks and reduce downtime at the ISP end itself.


Reliability
Prioritise critical applications with customisable QoS



Installation and maintenance
Our technicians can install network equipment and provide ongoing maintenance, including 24/7 support.
Do you know?






industry-leading SLAs






Countries Global Coverage with our strategic Partnership






Bandwidth Capacity






support






YEARS OF EXPERIENCE
Success Stories








Technology Partners